- Solutions
-
HARDWARE
Modernized Thin ClientsCompact, Energy-Efficient Devices for Remote Computing Access
Modernized Zero ClientsSecure Endpoints with No Local Storage for Seamless Integration
Endpoint MarketplaceFilter and view Modernized Thin Clients, Modernized Zero Clients, and Trusted Zero Clients with FREE Demo Access.
OPERATING SYSTEMS
10ZiG OS FamilyThe 10ZiG OS Family offers four Operating System options
SOFTWARE
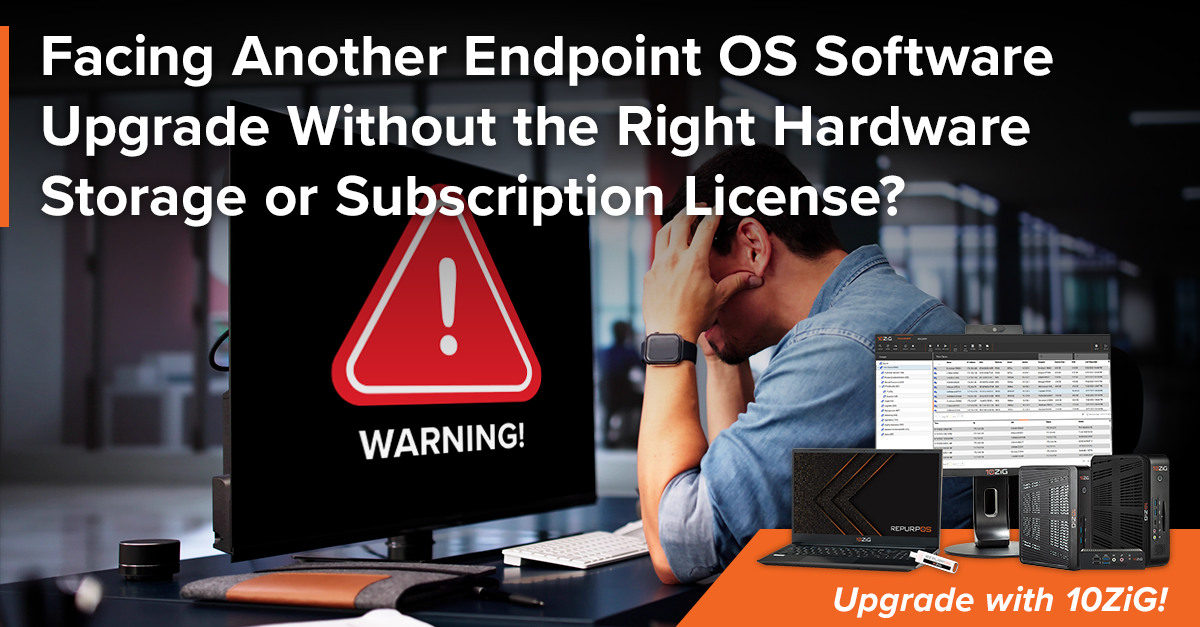
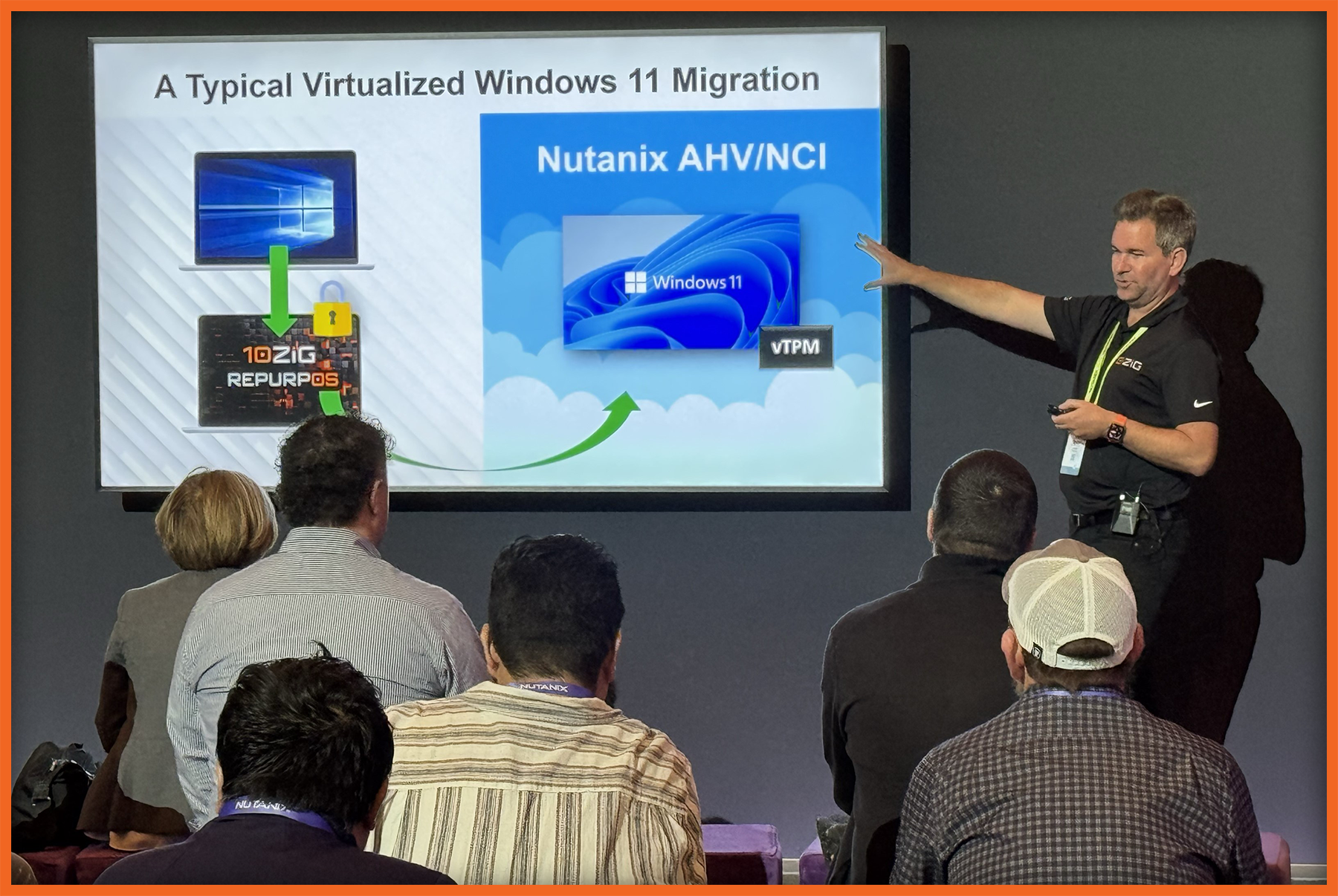
RepurpOSTransform Existing Hardware into Secure, High-Performance Virtual Endpoints
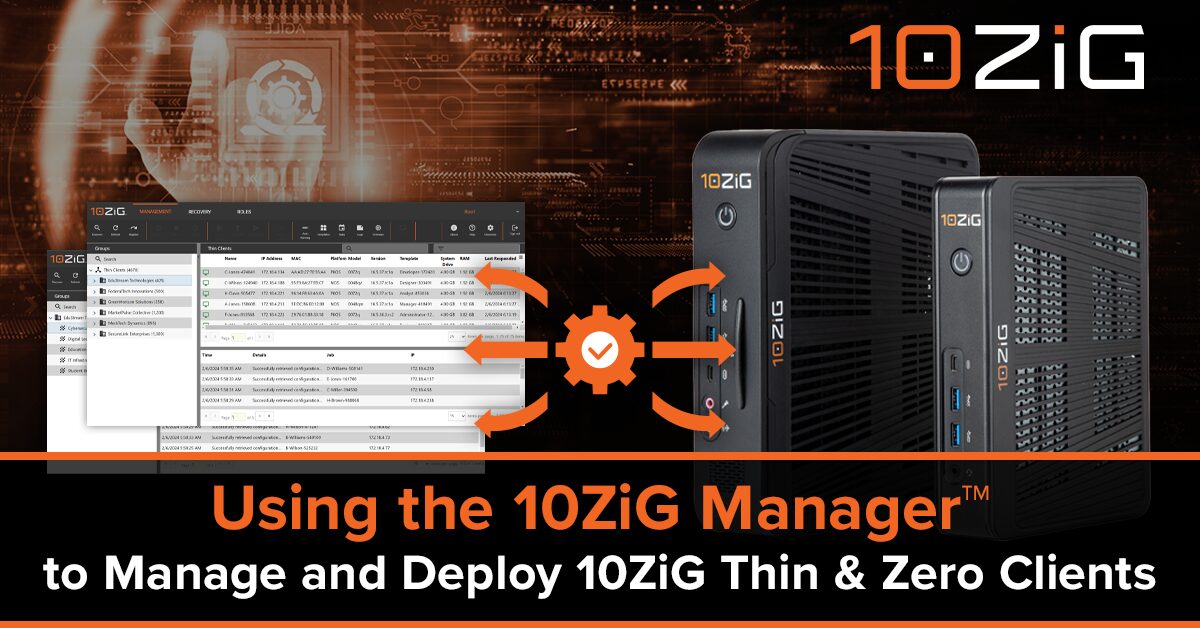
MANAGEMENT
The 10ZiG Manager™Streamline Endpoint Management with Our Free, Robust Software Solution
-
- Industries
- 10ZiG Ready Tech Partners
- FAQs
- Customer Support
- Resources
- Do not remove this link - This is for mobile version